I was an early adopter on Pinterest. I liked the service myself, not because I was looking for more social media, but because it allows me to aggregate links and sort them visually. I’m one of those people who navigate by landmarks, so having a visual cue reminds me which link goes to which article.
The problem is that the owners of Pinterest have been working to “improve” the site, often making it harder to use. Primarily adding more bells and whistles — that use more of my computers resources (internal memory). This makes it virtually impossible to use on my little underpowered netbook. (I can only have about 3 browser tabs open before it locks up.) So I usually do research on my big and powerful desktop computer, and the aggregate the links in Pinterest. I have an extensive link library I began to compile there during last years NaNoWriMo when I began my historical novel.
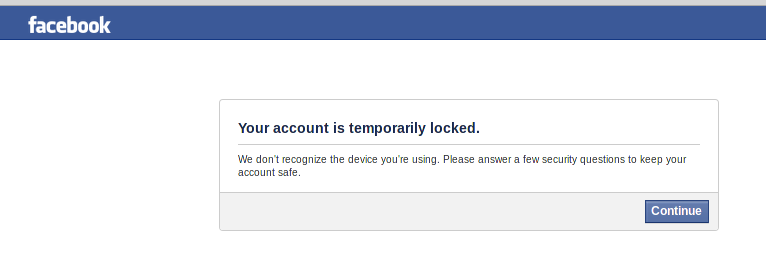
The problem is, Pinterest has recently crippled the service to anyone not signed in. This means I can’t just look at the site to find the link to the material I need, I have to sign in — and use more memory than I can afford — to access this. This is a huge problem for my own use of my own “pins.” But as someone who wants to share links to my own content, this means only people willing to sign in to Pinterest will be able to access my content. That’s a problem. I won’t be sharing Pinterest links anymore.
People concerned about personal privacy call that a registration wall. That’s a big part of why I stopped using Smashwords. I couldn’t use it for the purpose many authors use it — to give out free copies of ebooks — but if people have to pay Smashwords in personal information, the eBooks are not free at all. (Now I email review copies of ePubs, or people can anonymously download from TUEBL.)
And of course, there is Imgfave, another service that allows me to do much the same thing– without needing to be signed in to access my own (or anyone else’s) content. So that will do.
Who’s The Boss?
When we use someone else’s website, they get to make the rules, and we have to follow them. They can change how the site works, or what users are allowed to do, whenever they like. If we don’t like it, all we can really do is leave. (See: MySpace)
Pinterest is not alone in retaining control over how it chooses to allow us to use its website. The same is true of every other website that “generously” allows users to aggregate content or create content for its own greater glory (and profit). All we have to do is pay them in personal information and trust the faceless people making decisions not to change it to make it unusable for us.
Off the top of my head (but by no means an exhaustive list) web platforms that control your data can includes: Twitter, Facebook, G+, Pinterest, Imgfave, Instagram, dropbox, ScribD, NaNoWriMo, LibraryThing, GoodReads, MySpace, LinkedIn, DeviantArt, Imgur, Flickr, YouTube, Livestream, Wattpad, blogspot, WordPress.com, Tumblr, Livejournal etc.
DIY
 If you want to control your own data, you need to host it yourself. And that certainly will sound like a scary proposition. But is it any scarier that ripping up that carpet and replacing it with the tiles you want instead? We have no qualms about Do-It-Yourself projects in the physical world, it is not so much different in a digital world. Probably the biggest difference is that there are sure to be many more how-to videos on You-Tube for doing digital DIY. You can very often talk to actual people who made the software you need online via Twitter or through email. (Ever tried to ask Facebook a question?)
If you want to control your own data, you need to host it yourself. And that certainly will sound like a scary proposition. But is it any scarier that ripping up that carpet and replacing it with the tiles you want instead? We have no qualms about Do-It-Yourself projects in the physical world, it is not so much different in a digital world. Probably the biggest difference is that there are sure to be many more how-to videos on You-Tube for doing digital DIY. You can very often talk to actual people who made the software you need online via Twitter or through email. (Ever tried to ask Facebook a question?)
blogging
I know WordPress software is licensed to share, so you can download it to your own computer and host your own blog yourself, on your own computer. It is so easy lots of small businesses do this. WordPress even allows you to port your blog hosted on its free site to your own computer any time you like.
(Which is a great way to make backups… not because I don’t trust WordPress to do so, but because like any corporate service provider, it may be compelled to remove some or all of your content on receipt of a DMCA notice (a legal process that merely requires an accusation of copyright infringement… no proof needed). If your original work is taken down in this way, you will need to prove yourself innocent and then upload your content again. Backups are always a good idea because digital data is fragile. I am not certain but I think you can host your own Tumblr as well.
social media
If you are more interested in social media than blogging, there are a growing number of self hosting alternatives out there. If you like Facebook you might want to look at Friendica or Diaspora, if you like Twitter, you can host your own GNUsocial or StatusNet instance in the Fediverse. If you just want to be free of Twitter censorship, you can sign up for an account hosted by individual people, and there are a couple of big co-ops like Quitter and Gnusocial.de.
private browsing
I don’t know about you, but I don’t actually trust Google’s “private” browser to be private. And of course if you want more freedom from being tracked, you might want to use Duckduckgo or StartPage or Ixquick to do your web searches…
The only way to be private online is by using encryption (and even then you need to follow best practices). LONG passwords are more secure than a clever one that is difficult to type or remember.)
If you want to be secure, for email use PGP (stands for “Pretty Good Privacy”) the best (free) software; and for everything else, use TOR (TOR project). Great resources can be found at KW Crypto
And of course, you have the same problems if you use software that you don’t actually own… so Free Software is the way to go.
[Note: normally I would link everything but I simply don’t have time just now. Maybe later.]






 Most of us are in a position of having to trust others with our private data.
Most of us are in a position of having to trust others with our private data.